One of the largest cyberattacks in history, known as the WannaCry ransomware virus, is infecting computers worldwide. So far, the virus has infected over 200,000 computers in more than 150 countries.
HOW DOES THE VIRUS SPREAD?
The main way the virus infects computers is through a “phishing” email.
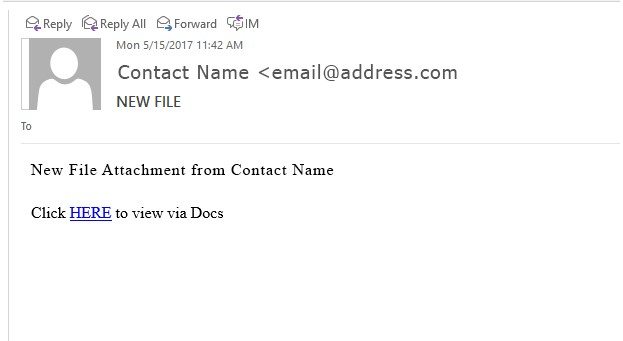
These type of emails can come from either a known or an unknown contact. In the email, you’ll receive a message that asks you to click on a link. The message may look innocent, but it’s meant to deceive you.
Here’s an example:
Clicking on the link gives the virus permission to download onto your computer. The virus then encrypts (hides) and locks all your files.
You may not notice the virus until important documents start disappearing. Shortly after, you’ll receive a pop up alert from the virus demanding money to decrypt and unlock the files. The only way to get the files back is to pay the “ransom.”
If you don’t pay within time, the ransom increases or the files disappear forever. The average pay out for the WannaCry virus was $300 per computer.
HOW CAN I PROTECT MYSELF?
Alert Employees
It is important to inform all staff about these suspicious emails.
If anyone receives this email, make sure they don’t click on the link, and instruct them to permanently remove it from the inbox.
If you, or an employee, is unsure if an email is legitimate, the safest practice is to call the sender to verify.
Install Updates & Patches
The WannaCry ransomware virus used a vulnerability in the Windows operating system. Microsoft learned about the vulnerability and created a patch on March 14, 2017 to fix the issue. People who installed the Microsoft patch remained protected from the virus, while the individuals that didn’t became vulnerable to the WannaCry virus.
You can ensure your servers and computers receive necessary updates and patches by using Strategy’s Managed Services.
Install an Antivirus Program
Install an Antivirus program on all computers, servers, and workstations (even Macs).
This helps protect your data and business against viruses and other malicious programs, which threaten operating systems and networks.
Configure Your Firewall with UTM
If your firewall settings aren’t properly installed and configured, then you may be more susceptible to having unauthorized access to your network.
We recommend using a firewall integrated with Unified Threat Management (UTM). This type of firewall performs multiple security functions:
- Monitoring network functions and performance
- Scanning traffic and programs accessing your network
- Preventing viruses or malware from accessing the system
Install a Datto Backup System
Whether you accidentally delete a file, or the operating system becomes corrupt, having a data backup system, like Datto, is crucial for disaster recovery and maintaining uptime.
Datto backup systems protect, secure, and restore your data in real time. The data retrieval takes a matter of hours rather than days. You can even run in virtual mode for minimal downtime.
Partner with Strategy
Learn more about best practices for your IT infrastructure on Strategy’s blog.
If you have any questions about the WannaCry virus, want to confirm your business is protected, or are interested in Managed Services, contact Strategy today.