A phishing scam is a malicious attack attempting to trick the target into entering sensitive information. The hacker behind the phishing attack is often trying to acquire user names and passwords for financial systems, credit card information, PayPal login information, or other personal information to be exploited at a later time.
Business Wire reported 91% of corporate phishing attacks try to trick the target by displaying a trusted name to the target so they are more likely to click the link in the email. We’ve seen these attacks become more sophisticated over time. Below we’ll show how sneaky these scams can be.
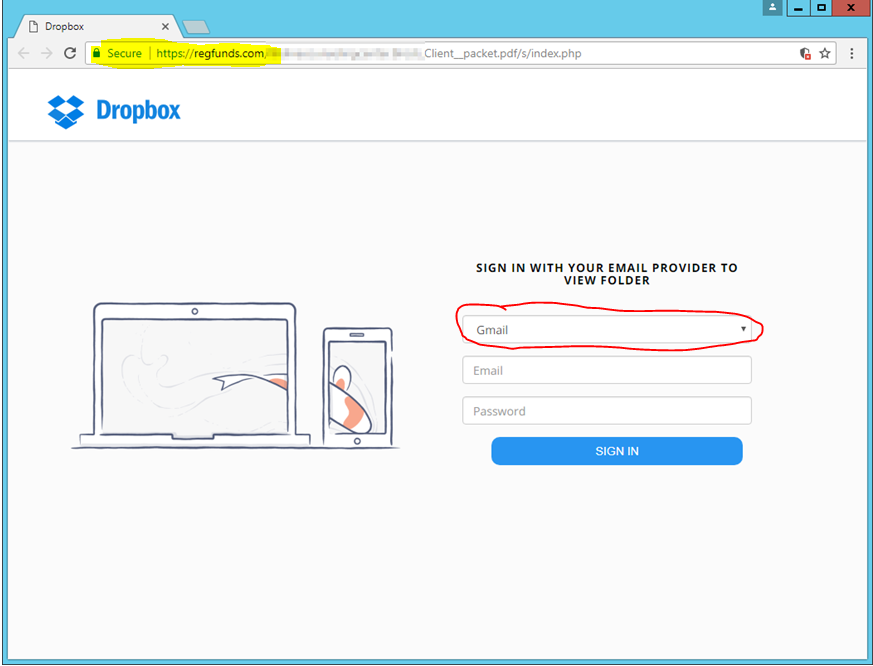
A hacker sent an original email with a PDF attachment from a hacked email account to all the contacts in the hacked users email system. The attachment itself was not infected, the email simply contained a request to login to the recipients Dropbox account and download the documents being sent. If the link was clicked, you went to the web page in the image below.
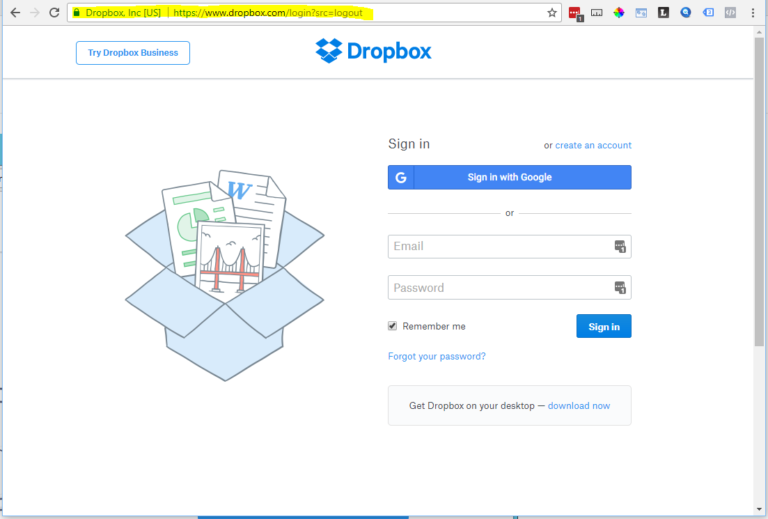
The fake website looks similar to the real dropbox.com website shown below. Note the difference in the highlighted URLs and the slight difference in the login fields on the actual DropBox page.
The first sign this was a phishing scam is the URL highlighted above, note the URL doesn’t go to www.dropbox.com, but to a website the hacker created to gather information. Next, the login fields are different than the actual Dropbox login fields.
In the fake site, the hacker is asking the target to select an email provider and then provide their login credentials to that email system. This is how the hacker is gaining access to various email accounts.
Once access is gained, the hacker can monitor emails for financial information, additional passwords, or other personal information. Additionally, they will have access to the targets contacts whereby they can send another phishing email attempting to trick even more people into providing information.
With these sophisticated attacks, how is it possible to protect your organization from phishing attacks?
Education & Training
The greatest defense against modern phishing attacks is a well-educated and trained staff.
As these attacks become more sophisticated, it is harder, if not impossible, for automated systems like firewalls and anti-virus systems to detect incoming attacks. Provide training to staff on how to detect phishing scams, avoid clicking links in emails, or opening attachments they are not expecting.
When an email appears to be suspicious, it’s always best to verify the user actually sent the email.
Continual Communication
In the craziness of the modern work day, we can forget to slow down and think critically about the emails we receive. That’s why it’s important to continually remind staff about malicious emails.
The costs of falling victim to a phishing attack can be catastrophic to your organization and staff. According to Symantec, 1 in 131 emails contains malware, with over 400 businesses targeted every day. In the last three years, phishing emails have cost businesses more than $3 billion.
Continually communicate safe email practices to your staff and encourage your IT staff to inform staff when attacks are happening or when a new popular attack is released.
Patch & Update Frequently
While many initial phishing attacks cannot be detected by automated systems, it’s still vital to keep your operating systems and other software patched for common security vulnerabilities.
Often the second step of a phishing attack is an attempt to install malware on the user’s computer. So keeping systems patched and updated is critical to avoiding the intended payload of a malware phishing attack.
Backup & Restore
In the event your systems are compromised, or breached, it is critical to have regular backups of your data and to routinely test the recovery and restoration process.
The number one source of ransomware attacks is from phishing emails. If ransomware is activated all data in your network could potentially be held for ransom, unless you have a solid backup and recovery plan.
The best backup systems provide local and off-site storage with virus protection. Skipping backups and restore processes can put your business, out of business.
Strong Password Protection
Implement strong password requirements for your users to help against a variety of brute force attacks and phishing scams. Set your user passwords to expire on a regular basis so if they are compromised, the scope of time will be limited.
We also encourage the use of password systems like LastPass to manage passwords and enforce an additional layer of security for your users. These password systems can help avoid password loss due to key-loggers and reduce user from accidentally entering a password into the wrong website.
Firewalls & AntiVirus
Having a business class Firewall with UTM (unified threat management) and current Anti-virus is critical to stop phishing attacks which intend to spread malware into your network. Avoid using home-based consumer products for your business, especially if you deal with PCI or HIPAA compliance.
Always Verify
The greatest security gap in phishing attacks is the human element and the best way to avoid an attack is to keep your staff educated and aware.
Encourage them to always verify the authenticity of a link or attachment. Does a link actually go to the domain it says it will (i.e. the dropbox example above), does the email have common grammar or misspellings (this is a dead giveaway that it’s phishing), does the offer sound too good to be true (the IRS found $100,000 in tax refunds for you), etc.
Always be aware, always verify.
So where do we go from here?
Phishing attacks became the number one source of malware and hacking attempts in 2016 and show no sign of slowing down.
Work with your staff to keep them educated and aware, make sure your systems are up to date and secure. If you need a partner to help with implementing these best practices, we’d love to work with you.
Enjoy content from Strategy? Make us one of your preferred sources on Google.